
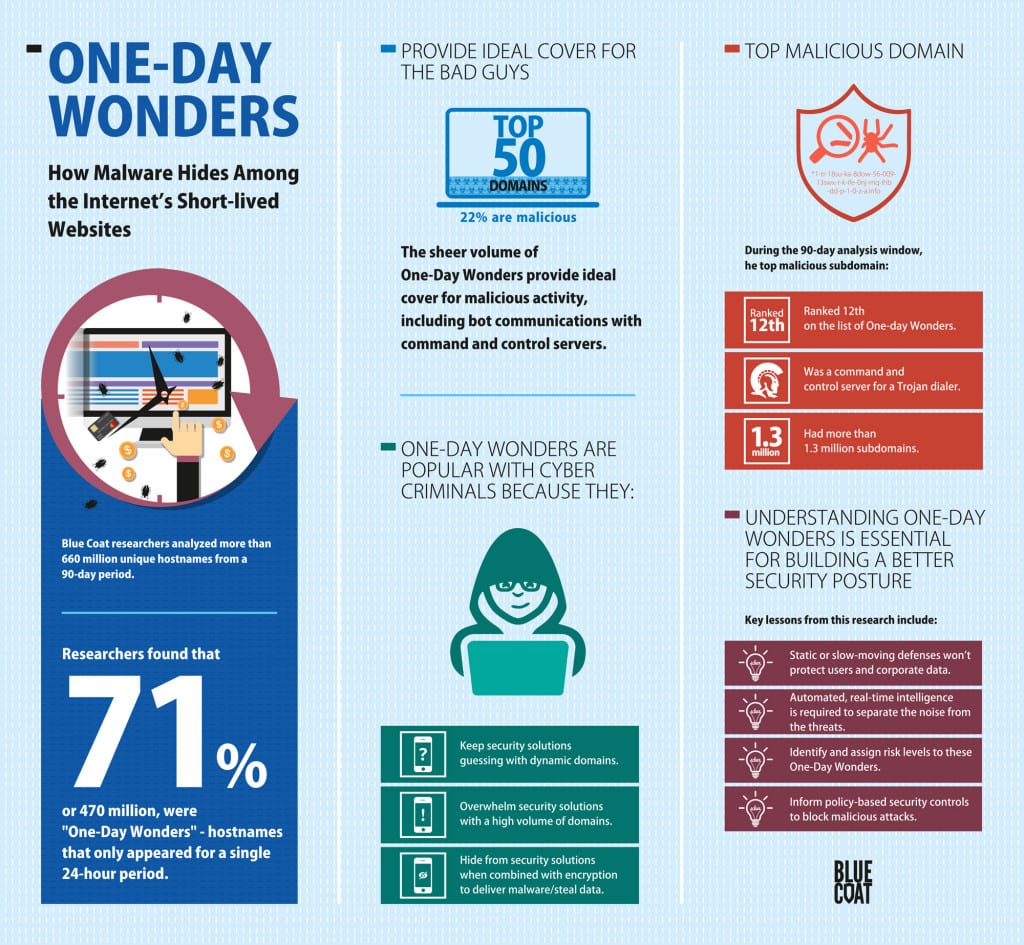
Blue Coat Systems, Inc., the market leader in business assurance technology, today announced that 71 percent of hostnames appeared for just 24 hours. While the majority of these “One-Day Wonders” are the backbone for how Internet content is shared and delivered, the sheer volume provides cover for malicious activity, including communication to infected systems. The new report from the Blue Coat Security Labs, “One-Day Wonders: How Malware Hides among the Internet’s Short-Lived Websites,” details the nature and activities of these rapidly appearing, and vanishing, destinations on the Web to better understand the security implications of websites that exist for less than 24 hours.
 The largest generators of One-Day Wonders include organizations that have a substantial Internet presence, such as Google, Amazon and Yahoo, as well as Web optimization companies that help accelerate the delivery of content. Blue Coat also found that in one case, one of the top ten most prolific creators of One-Day Wonders is the most popular pornography website on the Internet.
The largest generators of One-Day Wonders include organizations that have a substantial Internet presence, such as Google, Amazon and Yahoo, as well as Web optimization companies that help accelerate the delivery of content. Blue Coat also found that in one case, one of the top ten most prolific creators of One-Day Wonders is the most popular pornography website on the Internet.
Of the top 50 parent domains that most frequently used One-Day Wonders, 22 percent were malicious. These domains use short-lived sites to facilitate attacks and manage botnets, taking advantage of the site being “new and unknown” to evade security solutions. For example, One-Day Wonders can be used to build dynamic command and control architectures that are scalable, difficult to track and easy to implement. Alternatively, they can be used to create a unique subdomain for each spam email to avoid detection by spam or web filters.
“While most One-Day Wonders are essential to legitimate Internet practices and aren’t malicious, the sheer volume of them creates the perfect environment for malicious activity,” said Tim van der Horst, senior threat researcher for Blue Coat Systems. “The rapid building up and tearing down of new and unknown sites destabilizes many existing security controls. Understanding what these sites are and how they are used is a key to building a better security posture.”
One-Day Wonders are particularly popular with cyber criminals because they:
- Keep security solutions guessing: Dynamic domains are harder to thwart than static domains.
- Overwhelm security solutions: Generating a high volume of domains increases the chances that some percentage will be missed by security controls.
- Hide from security solutions: By simply combining One-Day Wonders with encryption and running incoming malware and/or outgoing data theft over SSL, organizations are typically blindto the attack, impacting their ability to prevent, detect and respond.
As organizations continue to fight ongoing battles against cyber attacks, they can draw key lessons from this research to inform and fortify their security posture, including:
- Security controls must be informed by automated, real-time intelligence that can identify and assign risk levels to these One-Day Wonders. Static or slow-moving defenses do not suffice to protect users and corporate data.
- Policy-based security controls must be able to act on real-time intelligence to block malicious attacks.
Blue Coat researchers analyzed more than 660 million unique hostnames requested by 75 million global users over a 90-day period. They found that 71 percent of the hostnames, or 470 million, were “One Day Wonders,” sites that appeared only for a single day.
Report and Infographic Available
To view a full copy of “One-Day Wonders: How Malware Hides among the Internet’s Short-Lived Websites,” please visit: https://www.bluecoat.com/security-report-one-day-wonders
A new infographic summarizing key findings is also available for download at: https://www.bluecoat.com/infographic-one-day-wonders